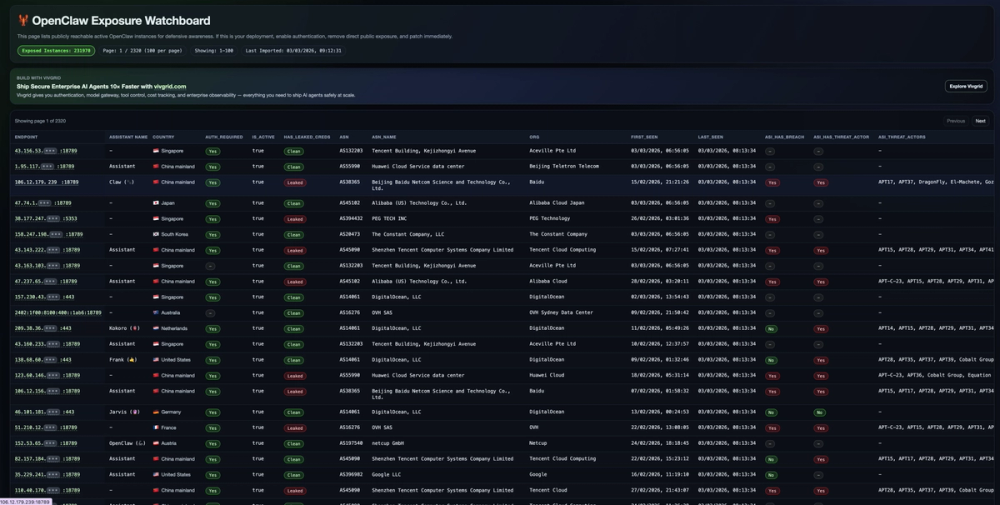
OpenClaw Exposure Watchboard: Enhancing Defensive Security Awareness
The OpenClaw Exposure Watchboard is a specialized online tool designed to provide critical visibility into the landscape of publicly accessible OpenClaw instances. Its primary objective is to bolster defensive security awareness by cataloging and presenting information about these exposed deployments. The platform serves as a vital resource for security professionals, system administrators, and organizations seeking to understand and mitigate potential risks associated with unsecured OpenClaw instances.
Understanding OpenClaw and its Exposure
OpenClaw is a framework or technology that, when deployed, creates instances that can be accessed over a network. The "Exposure Watchboard" specifically targets instances that are reachable from the public internet without proper authentication or security measures. This exposure can be a significant vulnerability, potentially allowing unauthorized access to sensitive data, system control, or exploitation of underlying software flaws. The watchboard aims to quantify this exposure by tracking the number of such instances and providing details about their location and status.
Key Features and Functionality
-
Real-time Instance Listing: The core functionality of the OpenClaw Exposure Watchboard is its ability to list actively exposed OpenClaw instances. This list is dynamically updated, providing users with the most current information available.
-
Defensive Security Focus: The platform is explicitly designed for defensive security purposes. It aims to alert users to potential threats and vulnerabilities by highlighting instances that lack essential security controls like authentication.
-
Instance Statistics: The watchboard provides valuable statistical data, including:
- Exposed Instances Count: A clear indicator of the scale of the problem, showing the total number of identified exposed instances.
- Pagination and Per-Page Display: For managing large datasets, the platform offers pagination, typically showing a set number of instances per page (e.g., 100).
- Current Page and Total Pages: Information about the user's current position within the dataset and the total number of pages available.
- Last Imported/Scanned Timestamp: Crucial for understanding the recency of the data, indicating when the information was last updated.
-
Detailed Instance Information: Each listed instance typically includes:
- Endpoint: The IP address and port of the exposed OpenClaw instance, often with a link to access it directly (though caution is advised).
- Assistant Name: The name or identifier of the specific OpenClaw assistant or service running on the instance.
- Country: The geographical location of the instance, identified by flag and name.
- Authentication Required: A clear indication of whether authentication is required for the instance (Yes/No or similar).
- Active Status: Whether the instance is currently considered active.
- Leaked Credentials Status: Information on whether the instance has been associated with leaked credentials, a critical security indicator.
- ASN (Autonomous System Number) and ASN Name: Details about the network provider hosting the instance.
- Organization (Org): The organization associated with the IP address.
- First Seen and Last Seen: Timestamps indicating when the instance was first detected and last observed.
- ASI (Advanced Security Information) Data: This section can include:
asi_has_breach: Indicates if the associated entity has been involved in a data breach.asi_has_threat_actor: Flags if the instance or its associated entity is linked to known threat actors.asi_threat_actors: Lists the specific threat actors associated with the instance.asi_cves: Lists any known Common Vulnerabilities and Exposures (CVEs) associated with the software or services running on the instance.asi_enriched_at: Timestamp for when the ASI data was last updated.asi_domains: Associated domains linked to the instance.
-
Search Functionality: The watchboard may include a search feature allowing users to look for specific endpoints by IP address, URL, or endpoint with a port.
-
Promotional Content: The platform also features promotional content for Vivgrid.com, highlighting its capabilities in building and managing secure AI agents at scale, emphasizing features like authentication, model gateway, tool control, cost tracking, and enterprise observability.
Target Audience and Use Cases
- Security Analysts and Researchers: To identify and analyze potential security risks, track the prevalence of exposed services, and gather threat intelligence.
- System Administrators and DevOps Engineers: To audit their own network infrastructure, ensure that their OpenClaw deployments are not publicly exposed without proper security, and to identify misconfigurations.
- Incident Responders: To quickly identify potentially compromised or vulnerable systems within their organization or in the broader internet landscape.
- AI/ML Operations Teams: To understand the security posture of AI agent deployments, especially those utilizing frameworks like OpenClaw.
Practical Applications and Benefits
- Vulnerability Identification: Proactively identify OpenClaw instances that are unintentionally exposed to the public internet, allowing for timely remediation.
- Risk Assessment: Quantify the risk associated with exposed instances by examining associated threat actor information and known vulnerabilities.
- Security Posture Improvement: Provides actionable data that can lead to better security practices, such as implementing robust authentication mechanisms and network segmentation.
- Threat Intelligence: Contributes to a broader understanding of the threat landscape concerning specific technologies like OpenClaw.
Technical Aspects
The OpenClaw Exposure Watchboard likely operates by continuously scanning IP address ranges and network ports associated with OpenClaw deployments. It leverages various data sources, potentially including network scanning tools, threat intelligence feeds, and vulnerability databases, to gather and correlate information. The use of ASN and organization data helps in attributing the exposed instances to specific entities. The inclusion of ASI data suggests a deeper level of security analysis, linking instances to known threats and vulnerabilities.
The website itself is built using Astro and likely employs modern web technologies for efficient data presentation and user interaction. The use of masked IP segments (e.g., 1.2.3.•••) is a common practice to obscure sensitive parts of an IP address while still providing enough information for identification, possibly for privacy or to prevent direct targeting without further investigation.
Conclusion
The OpenClaw Exposure Watchboard is a valuable tool for anyone concerned with the security of OpenClaw deployments. By providing a clear, data-driven overview of exposed instances, it empowers security professionals and administrators to take proactive steps to secure their systems and mitigate potential risks. Its detailed reporting, including threat actor and vulnerability information, makes it a powerful asset in the ongoing effort to maintain a strong cybersecurity posture in an increasingly interconnected digital world.